Most people think of Google Sheets as a place to track budgets or manage project timelines. Turns out, it’s also been quietly powering a global espionage operation.
Google just announced it dismantled a sophisticated cyberattack campaign called GRIDTIDE, run by a China-affiliated hacker group known as UNC2814. And the tool at the center of it all? A regular spreadsheet app you probably use every week.
Hackers Built a Backdoor Using the Google Sheets API
Here’s where things get genuinely clever, in a deeply unsettling way.
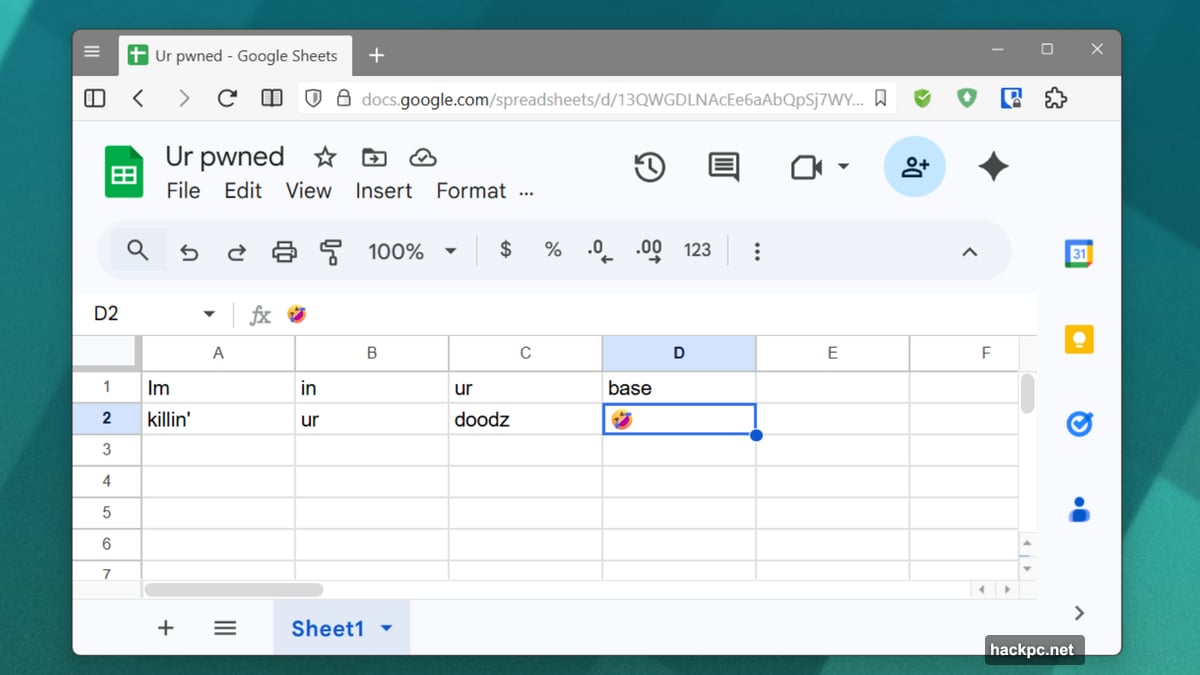
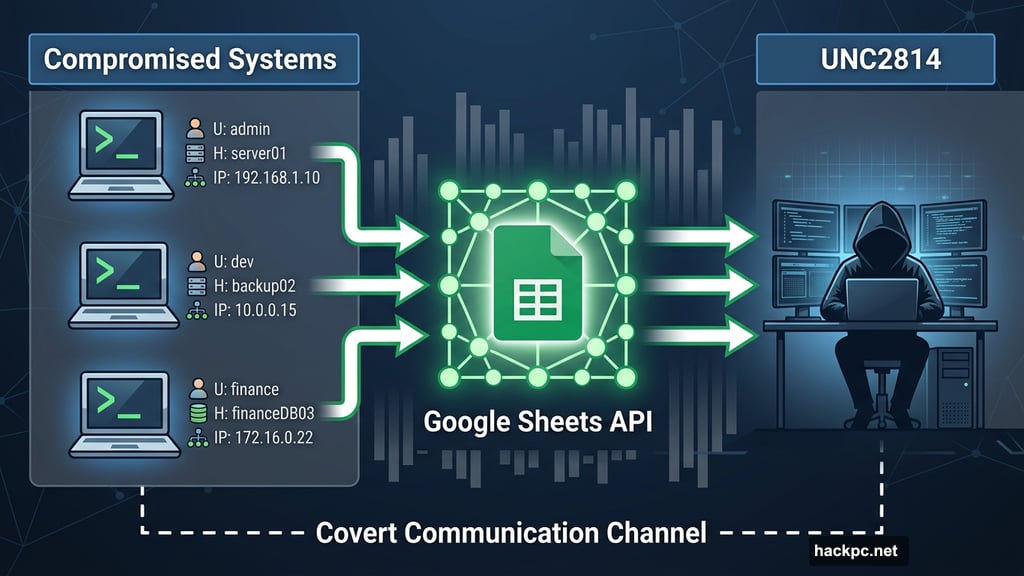
UNC2814 didn’t infect computers with traditional malware. Instead, they exploited the Google Sheets application programming interface (API) — the same interface that lets developers connect Sheets to other apps and services — to create a covert communication channel.
Through this backdoor, the group quietly harvested usernames, hostnames, and IP addresses from compromised systems. No dramatic ransomware. No obvious theft. Just silent, patient data collection hiding inside a tool that looks completely normal on any network.
GRIDTIDE Ran for Two Years Across 42 Countries
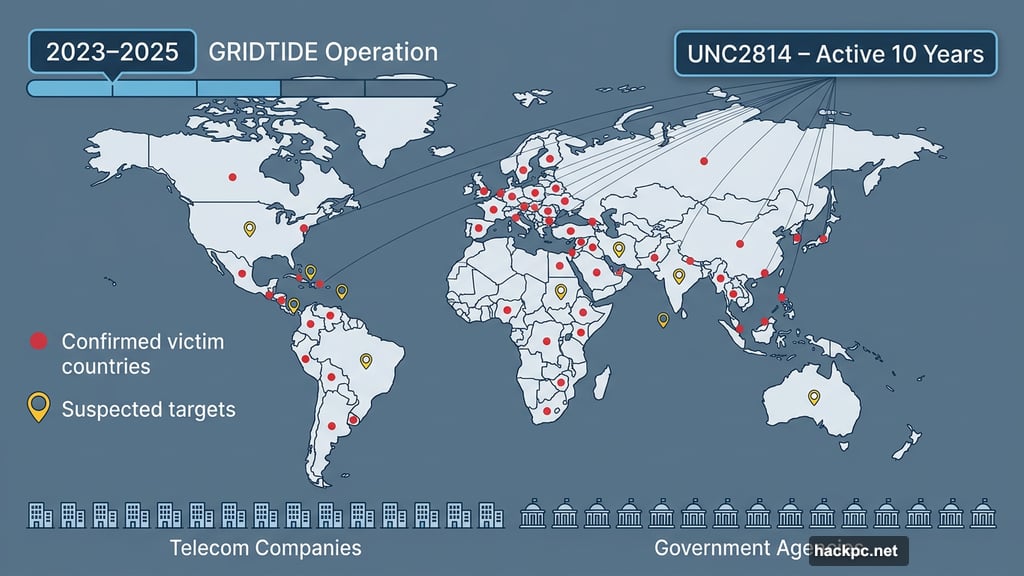
Google’s Threat Intelligence Group, which includes the Mandiant cybersecurity team acquired back in 2022, traced the GRIDTIDE operation back to 2023. By the time it was dismantled, the campaign had reached confirmed victims in 42 nations, with 20 additional countries suspected as targets.
Fifty-three specific organizations were hit. The primary targets were telecommunications companies and government agencies — exactly the kind of institutions that hold sensitive communications infrastructure and national security data.
Google describes UNC2814 as having operated for nearly a decade. So the scale of GRIDTIDE isn’t surprising. “This prolific scope is likely the result of a decade of concentrated effort,” the report notes.
Why State-Sponsored Espionage Loves Familiar Tools
This attack wasn’t about stealing money or crashing systems. It was pure intelligence gathering — the kind of long-game, low-noise operation that state-sponsored groups excel at.
That’s what makes GRIDTIDE so interesting from a security perspective. By routing activity through Google Sheets, attackers blended into normal business traffic. Security teams scanning for suspicious behavior would see familiar API calls, not obvious red flags.
It’s a reminder that threat actors don’t always need exotic, custom-built tools. Sometimes the most dangerous weapon is the one everyone already trusts.
Google Has Shut It Down — For Now
The good news is GRIDTIDE appears to be offline. Google’s Threat Intelligence Group shut down the accounts used to run the operation, along with the supporting domains and underlying infrastructure. Affected victims received formal notifications.
Whether UNC2814 rebuilds something similar using a different platform is the obvious follow-up question. Groups with a decade of operational experience don’t typically walk away after one takedown.
Still, disrupting an active espionage campaign spanning dozens of countries is a meaningful win. And it shows that tech companies actively monitoring their own platforms for abuse can catch threats that traditional security tools might miss.
The lesson here isn’t to stop using Google Sheets. It’s that no tool is too ordinary to become an attack vector — and that the most sophisticated threats often hide in plain sight.



Comments (0)