
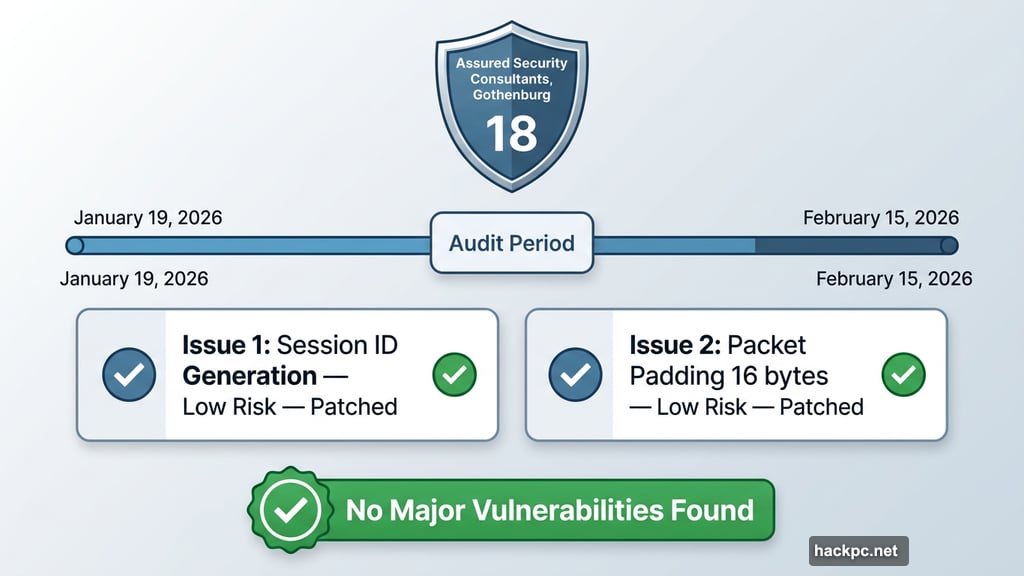
Mullvad VPN just completed its 18th independent security audit since 2017, and the results are about as good as you can hope for. No major vulnerabilities. Two minor issues, both already patched. And a clean bill of health for GotaTun, the company’s brand-new WireGuard implementation written in Rust.
For anyone who cares about online privacy, this is genuinely good news worth paying attention to.
What Is GotaTun and Why Does It Matter
Before jumping into the audit findings, it helps to understand what GotaTun actually is.
WireGuard is a VPN connection protocol — basically the method your device uses to create an encrypted tunnel to a VPN server. It’s fast, lightweight, and widely considered one of the best protocols available today. GotaTun is Mullvad’s own custom implementation of that protocol, coded from scratch in Rust.
The goal is simple: faster, more reliable connections for Mullvad users. GotaTun first landed in Mullvad’s Android app back in December 2025, with a broader rollout to other platforms planned for this year.

Writing your own implementation of an established protocol is a bold move. So naturally, you want someone to check the work.
What Assured Security Consultants Actually Tested
Gothenburg-based Assured Security Consultants ran the audit between January 19 and February 15, 2026. Their job was a deep source code review and full testing of the GotaTun implementation.
A couple of things were intentionally left out of scope. Mullvad’s DAITA code — the AI traffic analysis blocking feature — wasn’t included, nor was the command line interface. Everything else in GotaTun got a thorough look.
The verdict? No major vulnerabilities. Two low-risk issues flagged. Both have since been fixed.
The Two Issues Auditors Found
Neither issue is alarming, but both are worth understanding.
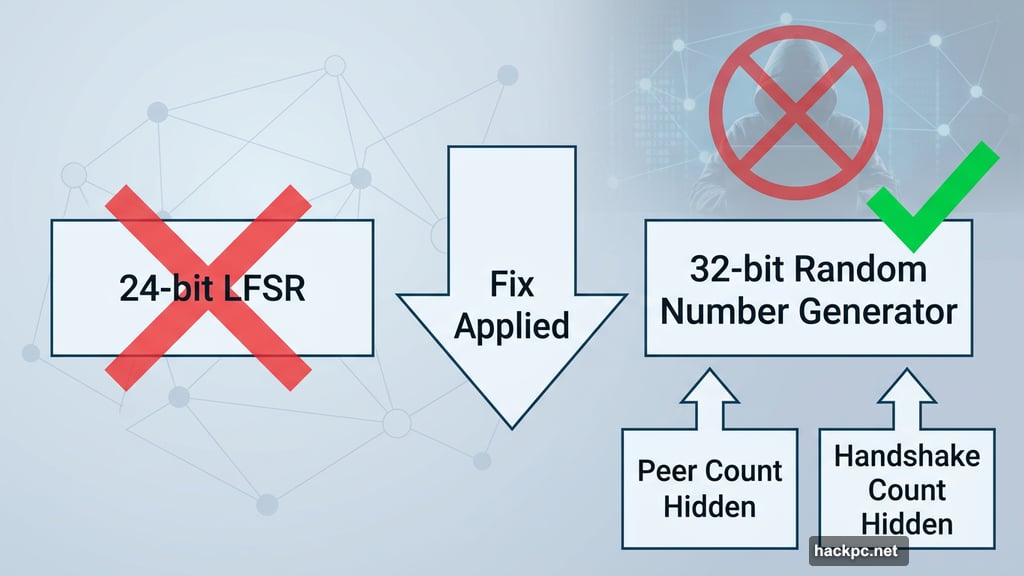
Issue one involved session identifier generation. GotaTun was generating session identifiers using a 24-bit Linear Feedback Shift Register. The WireGuard specification, however, calls for a 32-bit random number. Auditors noted this deviation could potentially reveal information about peer count and the number of handshakes to someone eavesdropping on network traffic.
Mullvad pushed back gently on the severity here. The company pointed out that an observer would already have access to total peer count and session duration through other means, making the practical risk extremely low. Still, they issued a fix anyway and now generate peer identifiers fully in line with WireGuard specifications.
Issue two was about packet padding. GotaTun wasn’t padding data packets to 16 bytes before encryption, which the WireGuard spec recommends. Auditors confirmed this wasn’t a cryptographic weakness, but suggested following the spec for consistency and completeness.
Mullvad fixed this too. The company did note, though, that the protection offered by this kind of padding is “somewhat similar in nature, but much less powerful” than their DAITA feature. If sophisticated traffic analysis is part of your threat model, Mullvad recommends switching DAITA on.
18 Audits in Nine Years Says Something
Audits matter in the VPN industry, but not all providers take them seriously. Mullvad does. Eighteen independent audits since 2017 puts the company among the most scrutinized VPN providers anywhere.
Among CNET’s top VPN picks, only ExpressVPN has commissioned more, with 23 audits since 2018. That’s a short list of providers willing to put their code in front of outside security researchers repeatedly and consistently.
It’s also worth noting that Mullvad’s software is fully open source. Anyone can inspect the code at any time. The independent audits on top of that aren’t strictly necessary — they’re a choice. And that choice says a lot about where Mullvad’s priorities sit.
Independent Audits Aren’t Perfect, But They Still Work
Here’s something worth being honest about. No security audit captures everything. Auditors can only validate what they find during the specific window they’re given. A clean audit doesn’t guarantee zero vulnerabilities in perpetuity.
But that doesn’t make audits useless — it makes them valuable in a different way. What audits do well is surface issues that might otherwise stay hidden for years. The two issues found in GotaTun were low risk, but they were real deviations from protocol specifications. Finding and patching them now, before a wide platform rollout, is exactly how this process is supposed to work.
Mullvad found two small gaps. Mullvad fixed two small gaps. That’s the cycle working as intended.
If you’re already using Mullvad, this audit should increase your confidence in GotaTun as it rolls out to more platforms. If you’ve been considering Mullvad but wanted reassurance about their security practices, this is probably the best kind of evidence you can ask for — a consistent, years-long track record of opening up their code to outside scrutiny and acting on what reviewers find.



Comments (0)