
Internet access isn’t guaranteed everywhere. For millions of people in Russia, Iran, and Myanmar, just opening a website can mean running into a government firewall. Amnezia, a Cyprus-based VPN company, just released something designed to help those people stay connected.
On Tuesday, Amnezia launched AmneziaWG 2.0, an update to its existing AmneziaWG protocol. The company calls it a “fundamental shift” in how the protocol works. And given where the internet is headed in several countries right now, the timing couldn’t be more urgent.
What Deep Packet Inspection Does to VPN Traffic
Before we get into how 2.0 works, it helps to understand what it’s fighting against.
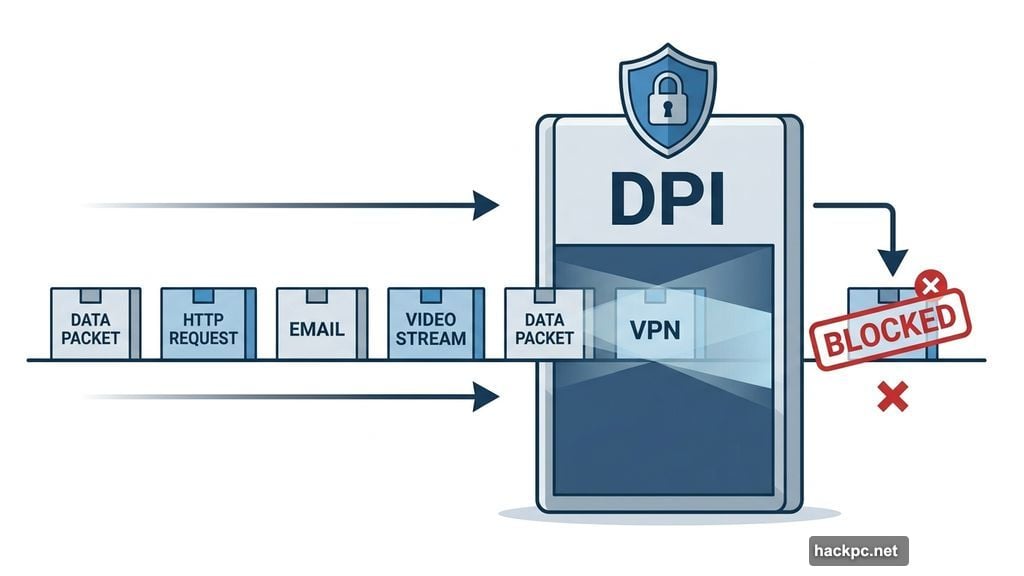
Governments with advanced censorship tools don’t just block websites anymore. Instead, they use a technique called deep packet inspection (DPI) to analyze the data traveling across their networks. Think of it like airport security for internet traffic — instead of just checking your ticket, they X-ray your bag.
Data travels across the internet in small chunks called packets. A VPN encrypts those packets, which sounds great. But DPI can sometimes identify the VPN protocol itself, even when the content is encrypted. Once a censor recognizes VPN traffic, they can block the connection entirely. Your VPN becomes useless.
So the real challenge isn’t just encrypting data. It’s making that encrypted VPN traffic look like something completely ordinary.
AmneziaWG 2.0 Mimics Everyday Internet Traffic
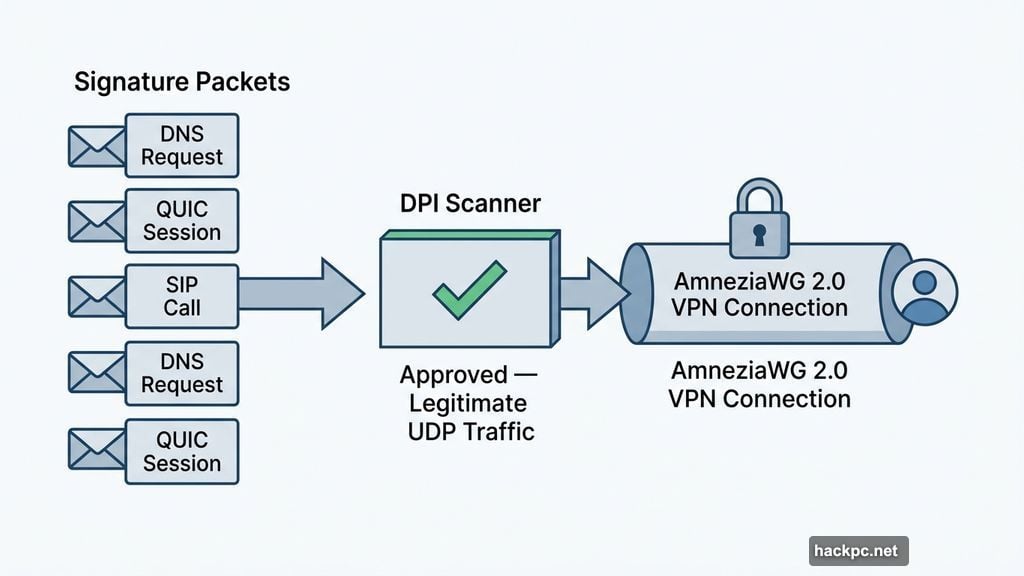
That’s exactly what Amnezia’s 2.0 protocol tries to do. Instead of looking like VPN traffic, it mimics legitimate internet activity — things like a DNS request, a QUIC session, or a SIP call. To a censor’s deep packet inspection tool, the connection looks completely normal.
The most significant innovation in version 2.0 is what Amnezia calls “signature packets.” The protocol sends up to five packets that imitate a standard network request. This tricks DPI systems into approving the connection. Then, once that initial handshake passes inspection, the real VPN connection begins underneath.
“In the second version, we kept some of the solutions from our first protocol but modified them to make the connection indistinguishable from legitimate UDP-based traffic,” Amnezia founder Mazay Banzaev told CNET.
The goal, he added, is to “stay ahead of the curve” when it comes to government censorship tools.
The Countries Driving This Development
Amnezia isn’t building this in a vacuum. The company has its largest user bases in Russia, Iran, and Myanmar — three countries where internet restrictions have become increasingly severe.
Russia, now four years into its war with Ukraine, continues cracking down on internet access. Iran is experiencing a near-total internet blackout following the start of its conflict with the US and Israel in March. Banzaev put it plainly: “Countries with censorship invest heavily in technologies to prevent users from visiting the open web. Today, they no longer just block specific websites in Iran — instead, they try to restrict much of the internet by default, leaving access only to those who are explicitly allowed.”
The scale of global internet censorship is striking. According to Surfshark’s Internet Shutdown Tracker, 17 Asian countries and nine African countries are currently restricting social media and messaging apps. Russia and Belarus rank as the two most censorship-heavy nations in Europe. Amnezia also reports growing interest from users in Africa, reflecting how widespread these restrictions have become.
What Makes Amnezia Different From Other VPNs
AmneziaWG is built on WireGuard, a widely-used VPN protocol that many other services rely on. But Amnezia adds extra layers of obfuscation on top. Those layers are what version 1.5 introduced, and what version 2.0 refines significantly.
This obfuscation focus is why WhatsApp actually recommended Amnezia by name in March, alongside Mullvad, as a VPN option for users who need to access the Meta-owned messaging app in restricted regions. That’s a meaningful endorsement from one of the world’s most-used communication platforms.
Amnezia is also open-source, which matters in this space. Open-source software lets independent researchers examine the code for security flaws or backdoors — something that’s especially important when the stakes involve personal safety in authoritarian environments.

The company offers a free tier, a premium plan ($28 for six months or $48 per year), a self-hosted option, and a business version. It currently serves 2.5 million monthly active users.
Why This Matters Beyond Tech Specs
It’s worth stepping back and thinking about what VPN obfuscation actually means for real people.
For someone in a US suburb, a VPN is a privacy tool or a way to watch foreign sports streams. For someone in Tehran or Moscow right now, it’s a lifeline. It’s how journalists communicate securely, how activists organize, and how ordinary people access news their governments don’t want them to see.
The arms race between censors and tools like Amnezia is genuinely high-stakes. And Amnezia’s 2.0 approach — disguising VPN traffic as mundane, everyday internet activity — represents a thoughtful response to how sophisticated government DPI tools have become.
Whether it stays ahead of those tools long-term remains to be seen. Censors adapt. Amnezia adapts back. That cycle isn’t ending anytime soon.
But for now, version 2.0 gives people in heavily restricted countries a better shot at staying connected. And that’s worth paying attention to.



Comments (0)