
Most people picking a VPN zero in on speed, price, and whether it unblocks Netflix. Those things matter, sure. But there’s one factor that affects your actual privacy more than almost anything else, and it barely gets mentioned: jurisdiction.
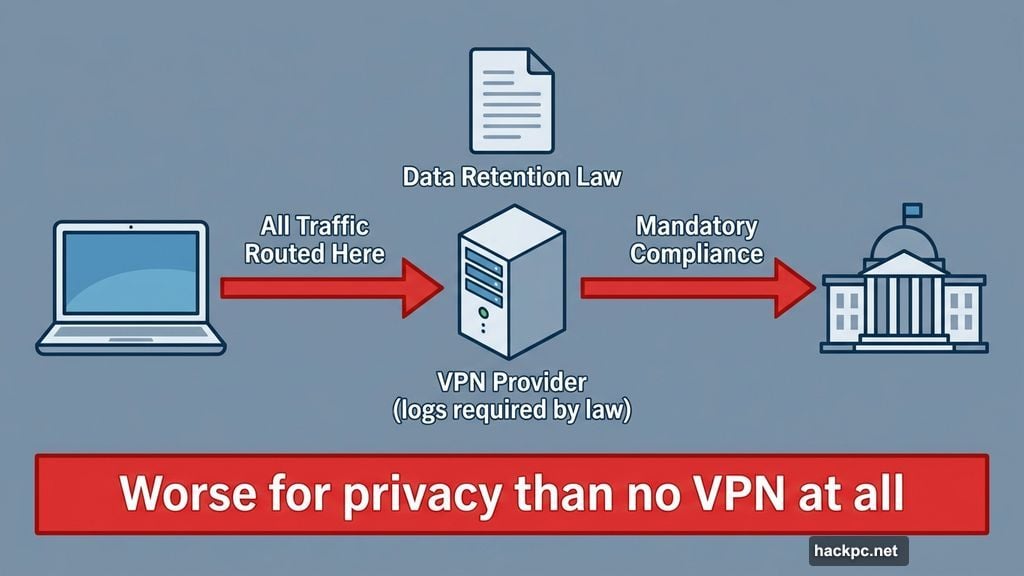
Jurisdiction means the country where your VPN company is legally registered. That country’s laws determine what data the VPN must collect, what requests from authorities it must comply with, and whether it can genuinely promise not to log your activity. Get this wrong, and you might as well not use a VPN at all.
In fact, using a VPN based in a country that legally requires user data logging is arguably worse for your privacy than using no VPN. You’re routing all your traffic through a service that may be required by law to record exactly what you’re doing.
Why the 14 Eyes Label Misleads People
You’ve probably heard the warnings. “Don’t use a VPN based in a 14 Eyes country!” The 14 Eyes is an intelligence-sharing alliance between 14 nations, and the concern is that member governments could demand your data from VPN companies inside their borders.
But here’s where things get nuanced. The Eyes designation matters far less than the specific data retention laws in each country.
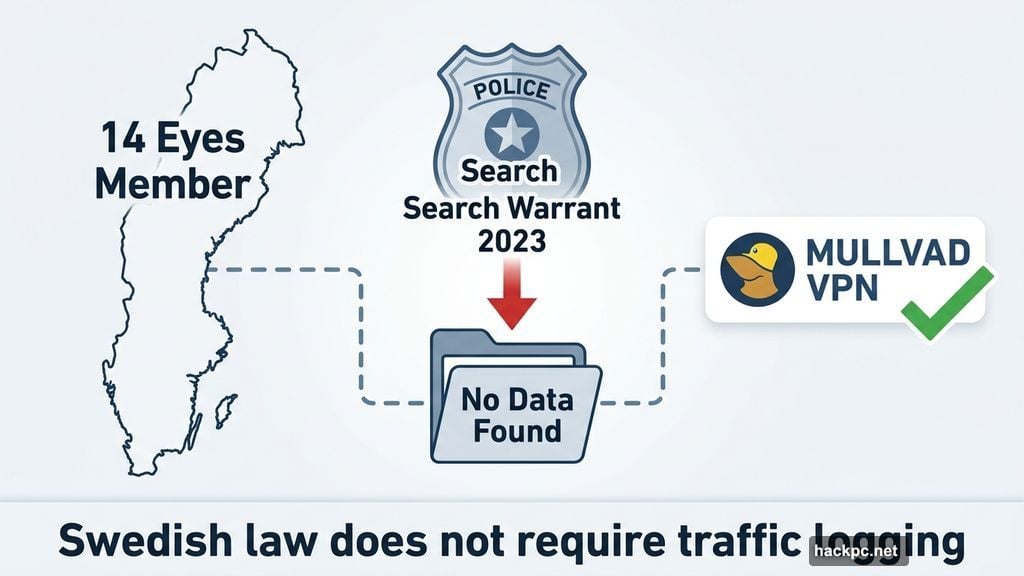
Take Mullvad, one of the most privacy-focused VPNs available. It’s based in Sweden, a 14 Eyes member. Yet Swedish law doesn’t force VPN providers to log user traffic. Swedish authorities have no legal tool to compel Mullvad to start recording what its users do online. And critically, foreign intelligence agencies from other 14 Eyes countries can’t simply reach across borders and demand that either.
Mullvad’s setup was tested for real in 2023. Swedish police showed up at Mullvad’s offices in Gothenburg with a search warrant, looking for customer data. They left empty-handed. The data didn’t exist because Mullvad genuinely doesn’t keep it.
Similarly, Windscribe operates out of Canada, another 14 Eyes country. Greek authorities came after Windscribe in 2023 over a separate investigation. That case was dropped in 2025 because there was no usable data to hand over. Dutch authorities reportedly seized a Windscribe server in February of this year, and that case is still ongoing. But Windscribe’s CEO told CNET that no user data is at risk, for the same reason: there’s nothing to hand over.
The lesson here is straightforward. What matters is whether local law can force a VPN to log. The Eyes number is a shortcut that oversimplifies a much more important question.
Jurisdictions That Raise Real Red Flags
Some countries carry genuine legal risks for VPN users, and it’s worth knowing which ones.
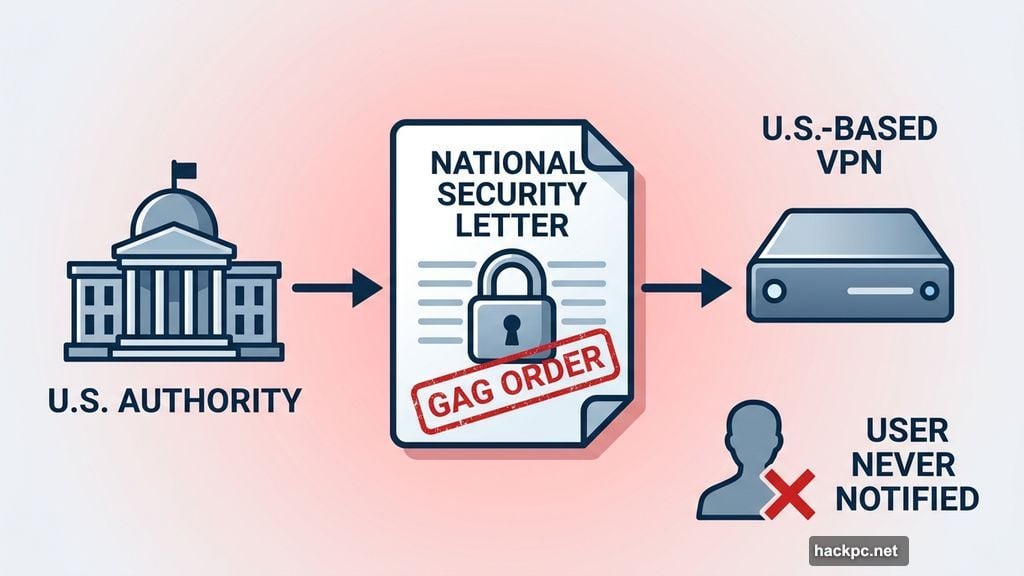
The United States is a concern because of national security letters. These are legal instruments that can force a company to hand over user records and, crucially, include a gag order preventing the company from ever telling anyone about it. A VPN in the US could theoretically be silently compelled to log data and prohibited from warning its users. There’s also an unresolved question making its way through US policy discussions: whether VPN users connecting to overseas servers are inadvertently waiving their constitutional protections against warrantless surveillance. Wired reported that US lawmakers recently sent a letter to the director of national intelligence asking exactly this question. If the answer turns out to be yes, the implications for US-based VPN users are significant.
The UK carries similar risk. The Investigatory Powers Act gives British authorities the power to weaken encryption, issue gag orders, and require ISPs, and potentially VPN providers, to retain user data. Australia has comparable laws that make VPNs registered there worth avoiding.
China sits in a category of its own. Any VPN legally operating in China must be government-approved and provide authorities with backdoor access. If a VPN is registered in China, that’s an immediate disqualifier for anyone who cares about privacy.
Where the Best VPNs Actually Live
The good news is that several jurisdictions have strong data protection frameworks without the coercive surveillance tools found elsewhere.
Switzerland is home to Proton VPN. Swiss law provides robust privacy protections, and authorities face significant legal barriers before they can compel tech companies to share data. Panama hosts NordVPN. Even though NordVPN’s offices are physically in Lithuania, the company is legally registered in Panama. Under Panamanian law, any data requests must follow Panamanian legal process. Gibraltar and Romania also offer favorable regulatory environments for privacy-focused businesses.
The British Virgin Islands, where ExpressVPN is registered, sits outside the reach of UK law despite the parent company, Kape Technologies, being headquartered in London. ExpressVPN’s privacy policy makes clear it operates under BVI laws, not UK ones. That distinction matters enormously.
Jurisdiction Alone Isn’t Enough
Good jurisdiction gets you halfway there. The other half comes from how a VPN is actually built.
RAM-only servers are a meaningful protection. Because these servers store nothing on a hard drive, every reboot wipes all data completely. There’s nothing to hand over even if authorities arrive with valid legal authority.
Open-source code matters too. If a VPN’s apps are publicly available for inspection, any hidden logging code would likely be spotted by independent researchers. Closed-source software offers no such assurance.
Regular third-party audits can’t verify every possible scenario, but they’re still important trust signals. They confirm that, at least at the time of the audit, a VPN’s infrastructure was set up consistently with its privacy claims.
Transparency reports, where VPNs publish the number and type of legal requests they receive each period and how they responded, help build track records over time.
Even with an unfavorable gag order in place, a truly privacy-focused VPN would struggle to flip a switch and start logging. Complying with a secret order to begin surveillance would require fundamentally rebuilding the server infrastructure and source code. That’s not something that happens quietly. And for open-source VPNs, any such changes would be visible to anyone examining the code.
Ownership Structures Can Be Confusing
One practical complication: some VPN companies are incorporated in one country, operated in another, and owned by a parent company based somewhere else entirely. That can make it hard to know which jurisdiction actually applies.
The rule of thumb is to look at where the VPN entity is legally registered and what its privacy policy says about which country’s laws govern it. Reputable VPNs make this clear. If a VPN is vague about where it’s registered or who owns it, that’s a reason to look elsewhere.
What to Actually Look For
When you’re evaluating a VPN for privacy, run through a short checklist. Is the VPN legally registered in a country without mandatory data retention laws? Does it have a no-logs policy that’s been independently audited? Has it ever been tested by real-world legal requests? Does it use RAM-only servers? Is its code open-source?
If the answer to most of those is yes, jurisdiction is working in your favor. If you can’t find answers, or the answers point toward the US, UK, Australia, or China, it’s worth thinking carefully before handing your traffic over to that service.
A trustworthy VPN shouldn’t just claim it won’t log your data. It should be legally registered somewhere that means it can’t be forced to.



Comments (0)