
Windows Recall was supposed to be fixed. After one of the messiest feature launches in Microsoft’s recent history, the company spent over a year rebuilding it from scratch. New security layers, biometric locks, an encrypted vault. Microsoft was confident it had addressed the concerns.
Then a security researcher built a tool that strips it all bare anyway.
What Windows Recall Actually Does
Before getting into the problem, it helps to understand what Recall is. Basically, it takes screenshots of nearly everything you do on your PC. Every document you open, every message you read, every website you visit. It then uses AI to make all of that searchable.
When Microsoft first announced Recall in 2024, the security community reacted sharply. Researchers called it a “privacy nightmare” and a cybersecurity “disaster.” The feature was pulled, reworked, and relaunched with significant protections baked in.
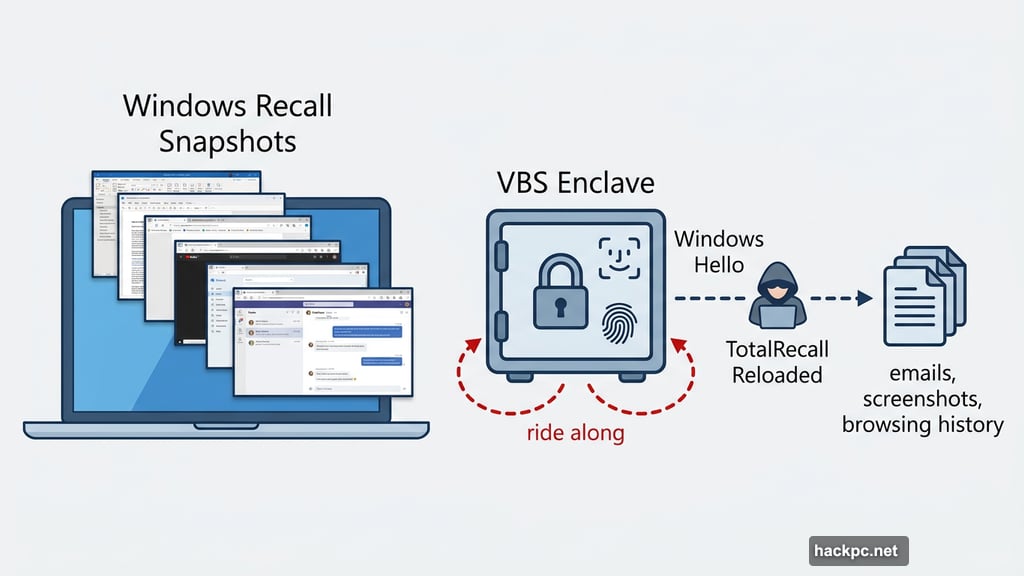
So what changed? Microsoft built a secure vault using Virtualization-based Security (VBS) Enclave technology. Recall now requires Windows Hello authentication, meaning a face scan or fingerprint, before it shows you anything or records new snapshots. Microsoft specifically stated this design “restricts attempts by latent malware trying to ride along with a user authentication to steal data.”
That last part matters a lot. Because a new tool suggests that protection doesn’t hold up.
TotalRecall Reloaded Bypasses the Security Vault
Cybersecurity researcher Alexander Hagenah built TotalRecall Reloaded, an updated version of the tool he originally created to expose weaknesses in the first Recall design. This new version targets the redesigned, supposedly more secure version.
Here’s how it works. The tool runs silently in the background. It activates the Recall timeline, which forces a standard Windows Hello authentication prompt to appear. The user authenticates normally, thinking nothing unusual is happening. At that point, TotalRecall Reloaded extracts everything Recall has ever captured.
Messages. Emails. Browsing history. Documents. Screenshots. All of it.
“My research shows that the vault is real, but the trust boundary ends too early,” Hagenah explains. “TotalRecall Reloaded makes that ‘latent malware’ ride along.” That’s the exact scenario Microsoft’s architecture was explicitly designed to prevent.
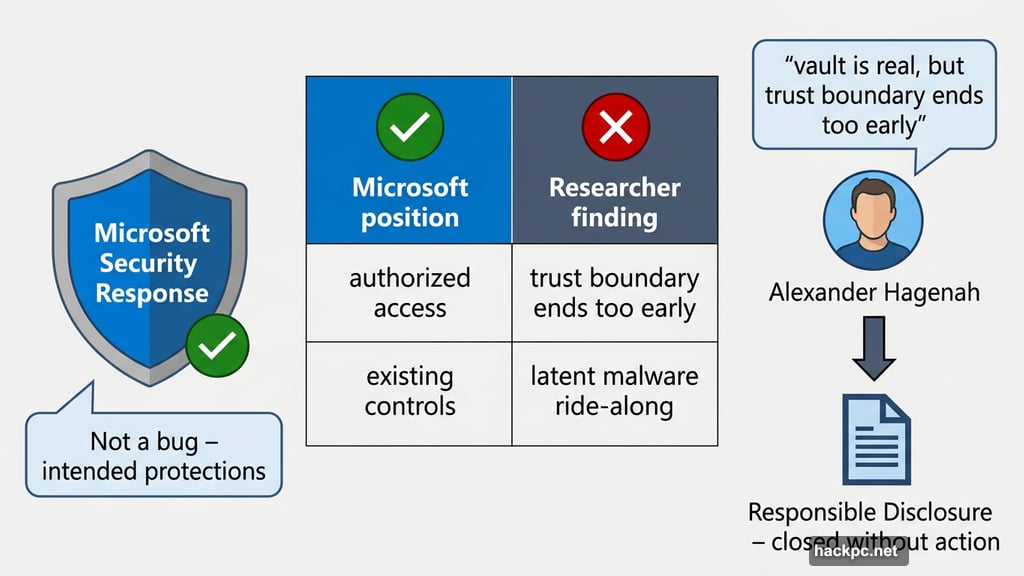
Microsoft Says It’s Not a Bug
Hagenah responsibly disclosed his findings to Microsoft last month. The company reviewed the report and closed it without action.
“After careful investigation, we determined that the access patterns demonstrated are consistent with intended protections and existing controls, and do not represent a bypass of a security boundary or unauthorized access to data,” said David Weston, Microsoft’s corporate vice president of enterprise and OS security, in a statement to The Verge.
Microsoft’s position is essentially this: what Hagenah demonstrated is how Windows works. Regular user-mode processes can inject code into other processes as a normal, often legitimate behavior. That flexibility also opens doors for abuse. But Microsoft considers that a general Windows behavior, not a specific Recall vulnerability.
The comparison they’d make is to infostealer malware that could silently extract data from a password manager like 1Password, or scrape your browsing history, if it slipped past your antivirus and other defenses.
Hagenah pushes back hard on that framing. And honestly, he has a point.
The Drywall Wall Problem
The issue isn’t that Microsoft’s security architecture is weak. Hagenah is actually quite clear that the technical foundations are solid.
“The VBS enclave is rock solid,” he says. “The authentication model is stateless and race-free.” After thousands of probes, he found zero bypasses of the core authentication system itself.
But here’s the gap. Once authentication succeeds and Recall decrypts its data, that decrypted content gets sent to an unprotected process for rendering. The data leaves the secure enclave and lands somewhere accessible to regular processes, including malicious ones running in the background.
Hagenah puts it perfectly: “The vault door is titanium. The wall next to it is drywall.”
He also disputes Microsoft’s claim about timeout protections. “I can re-poll the data, and what I am doing in my tool is to bypass it. And the timeout is patched out,” he says. Beyond full data extraction, TotalRecall Reloaded can also grab the latest cached Recall screenshot without any Windows Hello authentication at all, and it can wipe the entire capture history.
Why Recall Makes This Riskier Than Normal
Here’s the thing that separates Recall from a standard infostealer target. Recall aggregates an enormous amount of sensitive information in one place. Passwords, private messages, financial documents, personal conversations. All indexed, searchable, and now potentially accessible to a tool that can trigger authentication silently.
Yes, similar malware could target 1Password or your browser history. But those tools don’t capture everything. Recall does. That’s literally its selling point.
Microsoft CEO Satya Nadella told employees last year that if security ever comes into conflict with another priority, “your answer is clear: Do security.” The question Hagenah is raising is whether the current Recall architecture fully lives up to that commitment.
The good news is that this type of attack still requires malware to be running undetected on your machine. Microsoft’s existing security tools, including Windows Defender and memory protection features, are designed to catch exactly that. So the risk isn’t zero, but it’s not unlimited either.
Still, Hagenah’s argument is simple: if Recall’s specific design goal was to prevent malware from riding along on authentication, and a tool can demonstrably do exactly that, something in the design still needs fixing. Microsoft disagrees. For now, that disagreement is unresolved.



Comments (0)