The Vercel hack keeps getting worse. What started as a single, contained security incident now looks like something far more serious — and the full scope still isn’t clear.
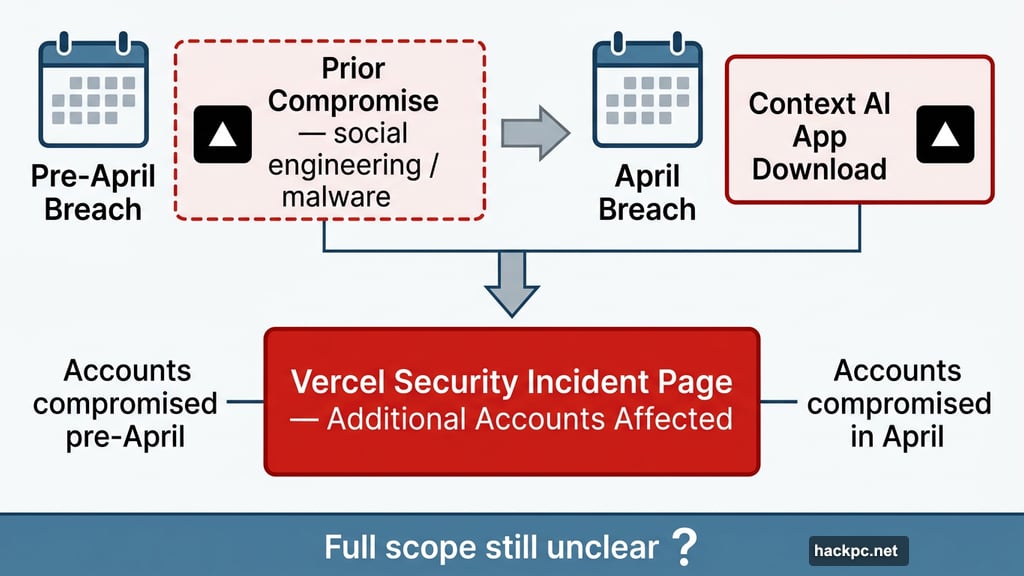
On Thursday, Vercel quietly updated its security incident page with news that should concern every developer using the platform. Hackers didn’t just breach the company in early April. Evidence suggests some customer accounts were already compromised before that breach ever happened.
That’s a very different kind of problem.
Prior Compromise Predates the April Breach

Vercel’s updated statement confirms the company found “a small number of customer accounts with evidence of prior compromise that is independent of and predates this incident.” The company says this earlier access may have come through social engineering, malware, or other methods.
So the timeline just got longer. Hackers may have had access to some customer data well before Vercel even knew anything was wrong. And Vercel won’t say how far back the second compromise dates.
Plus, the company also confirmed it found additional customer accounts affected by the April incident itself. It hasn’t disclosed how many, only that affected customers have been notified.
Infostealer Malware at the Center of It All
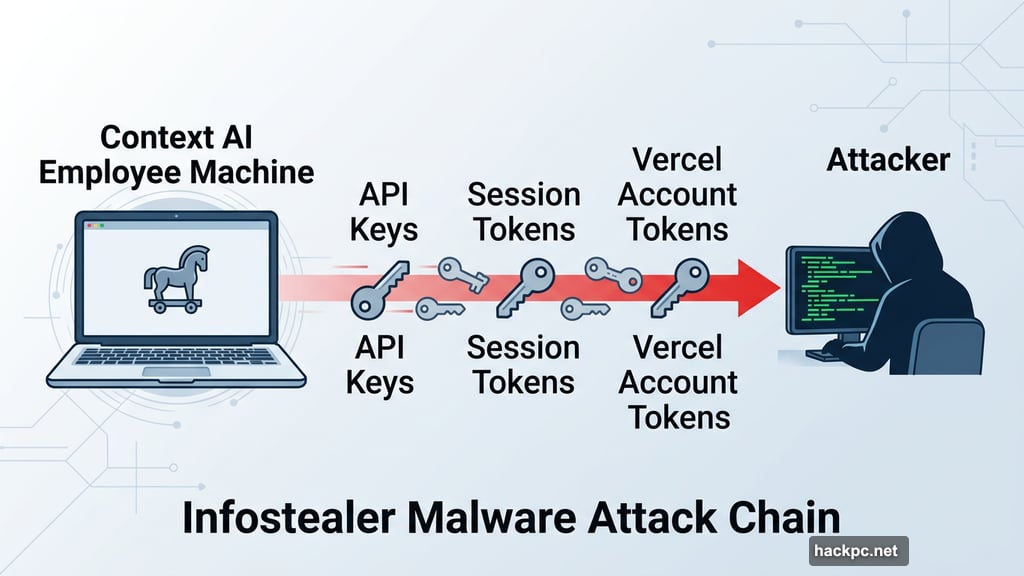
Vercel CEO Guillermo Rauch shared more details on X, and the picture he painted points to a well-known but nasty attack method: infostealer malware.
Think of infostealers as digital pickpockets. They disguise themselves as normal software. Once installed, they quietly scan your computer for anything valuable — passwords, session tokens, API keys, private access credentials. Then they send everything to the attacker.
In this case, Rauch says the malware targeted “tokens like keys to Vercel accounts and other providers.” Hackers then used those stolen keys to move fast. “Our logs show a repeated pattern: rapid and comprehensive API usage, with a focus on enumeration of non-sensitive environment variables,” Rauch wrote.
That kind of systematic, API-driven activity suggests the attackers knew exactly what they were doing. This wasn’t random. It was targeted.
The Context AI Connection Gets Messier
The original Vercel breach started because a Vercel employee downloaded an app built by a startup called Context AI. Hackers had already compromised Context AI’s systems and used that app to gain access to the employee’s work account — and from there, into Vercel’s internal systems.
But Rauch confirmed the hackers were active “beyond that startup’s compromise.” Context AI posted its own breach disclosure this week, confirming the earlier incident.
Security researchers have pointed to an interesting detail in all of this. A Context AI employee allegedly searched for Roblox game cheats and, in doing so, may have downloaded infostealer malware onto their work machine. That machine then handed hackers exactly what they needed to start pulling on threads.
It’s a reminder that major breaches rarely start with sophisticated attacks. Often, they start with one person, one download, one mistake.
Unencrypted Customer Credentials Made Things Worse
Here’s a detail that deserves more attention. The hijacked Vercel employee account gave hackers access to some internal systems — including customer credentials that were not encrypted.
That’s a serious problem on its own. Storing sensitive credentials without encryption removes a critical layer of protection. Even if an attacker gets in, encrypted credentials are far harder to misuse. Unencrypted ones are essentially ready to use immediately.
Vercel has not fully confirmed how the attackers first broke into its systems, and the company declined to comment beyond what appeared in the official update.
How Big Is This, Exactly?
Nobody knows yet. That’s the honest answer.
Both Vercel and Context AI have signaled that more victims could surface. The hackers appear to have been operating across multiple companies, not just these two. Security researchers and companies are still piecing together the full picture.
It’s also worth noting that TechCrunch reported separately that Delve — a compliance startup accused of faking customer data — performed the security certifications for Context AI. That raises its own set of questions about how much those certifications were actually worth.
For Vercel customers, the safest move right now is to rotate any API keys, access tokens, and credentials connected to your account. Don’t wait for Vercel to tell you whether you were affected. Treat your credentials as potentially exposed and start fresh.
The breach that started with a single app download has grown into something much larger. And based on what we know so far, there may be more surprises ahead.



Comments (0)